Pursuit vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
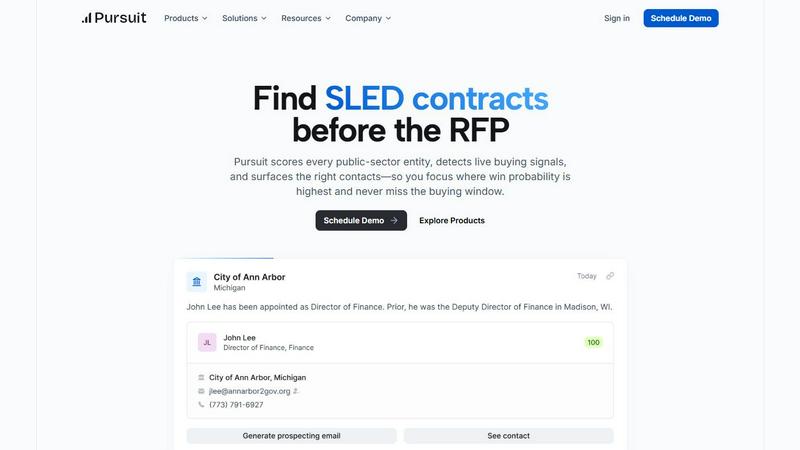
Pursuit
Pursuit uses AI to find and win public sector contracts before the RFP.
Last updated: February 28, 2026
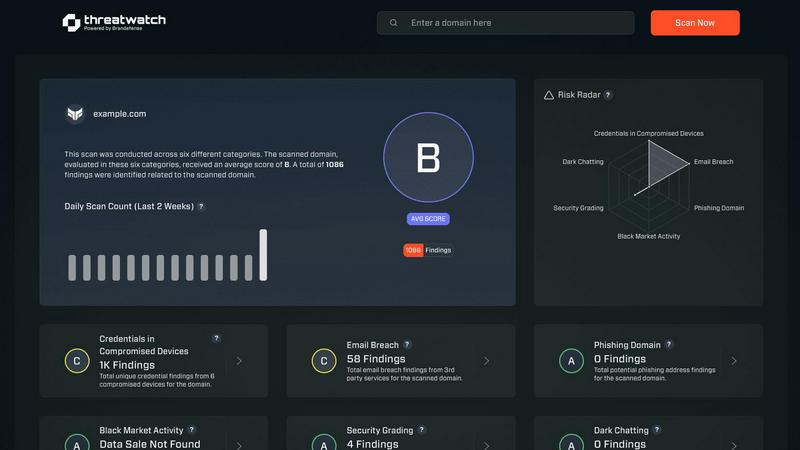
Threat Watch
Quickly assess your cybersecurity health with Threat Watch's actionable insights on compromised accounts and devices.
Last updated: March 1, 2026
Visual Comparison
Pursuit
Threat Watch
Feature Comparison
Pursuit
Real-Time Buying Signal Detection
Pursuit's AI engine scans and interprets millions of data points from across the SLED landscape, including budget documents, council meetings, and contract postings. It identifies concrete buying signals like budget approvals, new initiatives, leadership changes, and contract expirations, scoring entities on their buying propensity. This moves teams from reactive RFP chasing to proactive opportunity shaping based on live intelligence.
Automated CRM Data Enrichment
The platform ensures your customer relationship management system is always accurate and actionable. It provides auto-enriched accounts, contacts, and organizational charts with 94% data accuracy. Native, bi-directional integrations with Salesforce and HubSpot sync this refreshed intelligence automatically, eliminating manual data entry and reducing research time by 50% for operations teams.
Role-Specific Intelligence Workflows
Pursuit delivers tailored functionality for every persona in the revenue cycle. Account Executives get instant meeting prep via a Chrome extension. BDRs receive daily prioritized call lists. Marketing can build ABM campaigns around real budget cycles, and Customer Success gets configurable renewal alerts. This ensures every team member operates from the same, centralized intelligence.
Territory & Pipeline Visibility for Leaders
Sales leaders gain a comprehensive dashboard to see which reps are acting on which signals, identify coverage gaps, and forecast with confidence using real SLED buying indicators. This visibility into team activity and territory performance helps leaders optimize strategy and resource allocation to maximize pipeline growth and win rates.
Threat Watch
Comprehensive Cyber Health Assessment
Threat Watch provides a detailed evaluation of an organization’s cybersecurity posture by continuously scanning for vulnerabilities, compromised credentials, and potential threats, ensuring a holistic view of security health.
Automated Threat Intelligence
The platform automates the gathering and analysis of complex threat intelligence, reducing manual workload and providing real-time insights that help organizations identify emerging threats and assess their risk levels swiftly.
Prioritized Action Plan
By consolidating fragmented threat data, Threat Watch generates a single prioritized action plan. This enables organizations to focus on the most critical risks and respond effectively to mitigate potential damage.
Dark Web Monitoring
Threat Watch continuously monitors dark web activities to identify compromised credentials and breached accounts, allowing organizations to take immediate action to protect their assets from potential exploitation.
Use Cases
Pursuit
Proactive Pipeline Generation for BDRs
Business Development Representatives stop cold calling blindly. Pursuit provides daily alerts on high-intent signals within their territory, such as budget approvals or contract expirations. This allows BDRs to build prioritized outreach lists with relevant context, leading to more meaningful conversations and a documented 47% increase in qualified SLED pipeline.
Strategic Account Planning for AEs
Account Executives eliminate pre-call research scrambles. With the Pursuit Chrome extension, they instantly access a full account dossier before every meeting, including known incumbents, contract history, procurement vehicles, and recent signals. This preparation allows them to show up as a trusted advisor, contributing to a 32% improvement in win rates.
Targeted ABM Campaign Creation for Marketing
Marketing teams move beyond firmographics to signal-based targeting. Pursuit identifies in-market accounts based on concrete budget cycles and new initiatives. Marketers can then build and execute hyper-relevant account-based marketing campaigns, syncing audiences directly to platforms like LinkedIn, Marketo, or HubSpot, achieving a 2.4x lift in campaign conversion rates.
Renewal Risk Management for Customer Success
Customer Success managers gain early visibility into renewal and churn risks. The platform monitors for signals like budget cuts, leadership changes, or competitor RFPs at existing accounts, sending configurable alerts 90-180 days before renewal. This enables proactive retention strategies and leads to a 3x faster renewal identification process.
Threat Watch
IT Security Monitoring
IT security teams can leverage Threat Watch to continuously monitor their digital assets for vulnerabilities and threats. The platform provides real-time alerts, helping teams respond swiftly to emerging risks.
Risk Management
Risk managers can use Threat Watch to assess the overall cybersecurity health of the organization. The actionable insights provided enable informed decision-making and risk prioritization to protect sensitive data.
Incident Response Planning
Organizations can utilize Threat Watch to develop effective incident response plans. The platform’s real-time threat intelligence assists teams in preparing for potential security incidents, minimizing response times and impact.
Compliance Assurance
Threat Watch aids organizations in maintaining compliance with industry regulations by providing comprehensive assessments of cybersecurity practices. This ensures that organizations meet required standards while safeguarding their data.
Overview
About Pursuit
Pursuit is the definitive pre-RFP intelligence platform for companies selling to state, local, and education (SLED) governments. It transforms the traditionally slow, opaque, and relationship-dependent public sector sales process by delivering real-time data and actionable buying signals. The platform continuously monitors over 110,000 public entities, analyzing documents, meeting minutes, and budget cycles to detect live procurement intent 6-18 months before a formal RFP is issued. This allows sales, marketing, and operations teams at government contractors and technology vendors to identify and engage with high-propensity accounts at the exact right time. By providing enterprise-level research, automated CRM enrichment, and role-specific workflows, Pursuit acts as a force multiplier for entire go-to-market teams. Its core value is enabling businesses to build pipeline proactively, show up as the informed incumbent, and win more SLED deals by focusing efforts on relevance and timing, not just relationships.
About Threat Watch
Threat Watch is a unified cybersecurity intelligence platform that empowers organizations to gain a clear and actionable view of their digital security posture. Designed for IT security teams, risk managers, and business leaders, it shifts the focus from reactive security to proactive risk management. Threat Watch continuously analyzes an organization's assets, vulnerabilities, and exposures across critical security categories, providing a comprehensive cyber health assessment. Its core value proposition lies in its speed and clarity; the platform automates intricate threat intelligence gathering and analysis, delivering real-time insights. This enables users to identify, prioritize, and mitigate risks more efficiently. By consolidating data on compromised credentials, breached accounts, phishing addresses, and dark web exposures, Threat Watch transforms fragmented threat data into a prioritized action plan, ensuring organizations can act quickly to safeguard their digital environments.
Frequently Asked Questions
Pursuit FAQ
What types of buying signals does Pursuit detect?
Pursuit detects a wide range of concrete, early-stage buying signals from public documents and data. This includes mentions of new initiatives or projects in meeting minutes, budget approvals for specific technology categories, contract expiration dates, leadership changes in relevant departments, and the posting of early-stage RFIs or sources sought notices, often 6-18 months before an RFP.
How does Pursuit ensure data accuracy and freshness?
The platform employs continuous automated monitoring of over 110,000 SLED entity sources. Its AI is trained to extract and interpret data from unstructured documents. Combined with a proprietary data enrichment engine, Pursuit maintains a 94% data accuracy rate. All account and contact information is refreshed and synced bi-directionally with your CRM in real-time, ensuring teams always have the latest intelligence.
Can Pursuit integrate with our existing tech stack?
Yes. Pursuit is built for seamless integration. It offers native, bi-directional integrations with major CRMs like Salesforce and HubSpot, requiring no engineering effort to set up. It also supports audience sync with marketing platforms such as Marketo, HubSpot, and LinkedIn Ads, allowing signals to flow directly into your existing workflows and campaigns.
Is Pursuit only for large government contractors?
No. Pursuit is designed for any company selling products or services to the SLED market, from fast-growing startups to established enterprise contractors. The platform scales to meet different needs, providing the same critical early intelligence to level the playing field and help smaller companies compete effectively by finding opportunities before larger, slower-moving incumbents.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, including those in finance, healthcare, and technology sectors, where cybersecurity is critical to protecting sensitive information and maintaining compliance.
How does Threat Watch automate threat intelligence?
The platform utilizes advanced algorithms and machine learning to automate the collection and analysis of threat data from various sources, significantly reducing the time and effort required for manual threat assessments.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to integrate seamlessly with existing cybersecurity tools and platforms, allowing organizations to enhance their security posture without disrupting current workflows.
What is the process for starting with Threat Watch?
Organizations can easily initiate a free scan through the Threat Watch platform. This initial assessment provides valuable insights into their cybersecurity health, helping them understand their risk landscape.
Alternatives
Pursuit Alternatives
Pursuit is an AI-powered sales intelligence platform designed for businesses selling to state, local, and education (SLED) government entities. It helps teams find and win contracts by detecting early buying signals before an RFP is issued. Users may explore alternatives for various reasons, such as budget constraints, a need for different feature sets, or a preference for a platform that integrates with a broader range of sales tools. The search for a different solution is a normal part of finding the right fit for a company's specific sales process and goals. When evaluating alternatives, key considerations should include the depth and accuracy of public-sector data, the ability to provide proactive alerts on live opportunities, and how well the platform integrates with your existing CRM and sales workflow to drive efficiency.
Threat Watch Alternatives
Threat Watch is a comprehensive cybersecurity intelligence platform that empowers organizations to assess their digital security health with actionable insights. Designed for IT security teams, risk managers, and business leaders, it automates complex threat intelligence gathering and offers real-time assessments of vulnerabilities and exposures. Users often seek alternatives due to factors such as pricing, unique feature sets, or specific platform compatibility needs that better align with their organizational goals. When considering alternatives, look for platforms that provide robust threat intelligence, real-time monitoring capabilities, and an intuitive user interface. It's essential to evaluate the comprehensiveness of the cyber health assessments and whether the solution can effectively prioritize risks based on severity and context to ensure proactive risk management.
