Threat Watch
Quickly assess your cybersecurity health with Threat Watch's actionable insights on compromised accounts and devices.
AI tool Details
Explore More
Alternatives
About Threat Watch
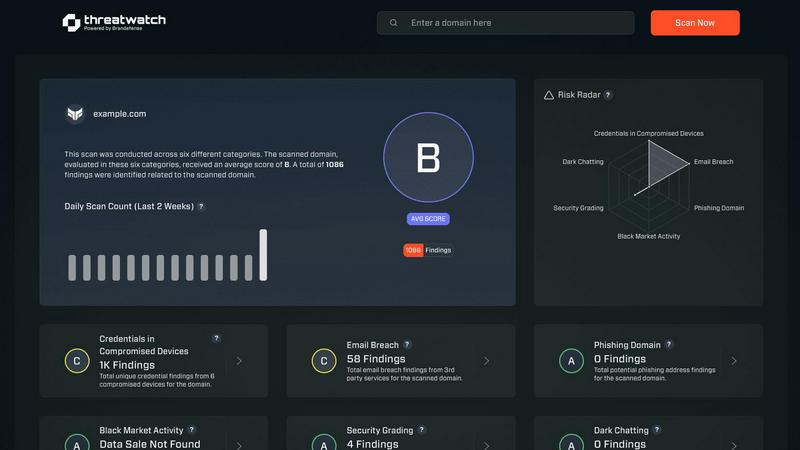
Threat Watch is a unified cybersecurity intelligence platform that empowers organizations to gain a clear and actionable view of their digital security posture. Designed for IT security teams, risk managers, and business leaders, it shifts the focus from reactive security to proactive risk management. Threat Watch continuously analyzes an organization's assets, vulnerabilities, and exposures across critical security categories, providing a comprehensive cyber health assessment. Its core value proposition lies in its speed and clarity; the platform automates intricate threat intelligence gathering and analysis, delivering real-time insights. This enables users to identify, prioritize, and mitigate risks more efficiently. By consolidating data on compromised credentials, breached accounts, phishing addresses, and dark web exposures, Threat Watch transforms fragmented threat data into a prioritized action plan, ensuring organizations can act quickly to safeguard their digital environments.
Features
Comprehensive Cyber Health Assessment
Threat Watch provides a detailed evaluation of an organization’s cybersecurity posture by continuously scanning for vulnerabilities, compromised credentials, and potential threats, ensuring a holistic view of security health.
Automated Threat Intelligence
The platform automates the gathering and analysis of complex threat intelligence, reducing manual workload and providing real-time insights that help organizations identify emerging threats and assess their risk levels swiftly.
Prioritized Action Plan
By consolidating fragmented threat data, Threat Watch generates a single prioritized action plan. This enables organizations to focus on the most critical risks and respond effectively to mitigate potential damage.
Dark Web Monitoring
Threat Watch continuously monitors dark web activities to identify compromised credentials and breached accounts, allowing organizations to take immediate action to protect their assets from potential exploitation.
Use Cases
IT Security Monitoring
IT security teams can leverage Threat Watch to continuously monitor their digital assets for vulnerabilities and threats. The platform provides real-time alerts, helping teams respond swiftly to emerging risks.
Risk Management
Risk managers can use Threat Watch to assess the overall cybersecurity health of the organization. The actionable insights provided enable informed decision-making and risk prioritization to protect sensitive data.
Incident Response Planning
Organizations can utilize Threat Watch to develop effective incident response plans. The platform’s real-time threat intelligence assists teams in preparing for potential security incidents, minimizing response times and impact.
Compliance Assurance
Threat Watch aids organizations in maintaining compliance with industry regulations by providing comprehensive assessments of cybersecurity practices. This ensures that organizations meet required standards while safeguarding their data.
Frequently Asked Questions
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, including those in finance, healthcare, and technology sectors, where cybersecurity is critical to protecting sensitive information and maintaining compliance.
How does Threat Watch automate threat intelligence?
The platform utilizes advanced algorithms and machine learning to automate the collection and analysis of threat data from various sources, significantly reducing the time and effort required for manual threat assessments.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to integrate seamlessly with existing cybersecurity tools and platforms, allowing organizations to enhance their security posture without disrupting current workflows.
What is the process for starting with Threat Watch?
Organizations can easily initiate a free scan through the Threat Watch platform. This initial assessment provides valuable insights into their cybersecurity health, helping them understand their risk landscape.
Similar to Threat Watch
AI Business Name Generator
Instantly create unique and catchy business names for startups and brands with our free AI Business Name Generator.
FormRoyale
Run Smarter Surveys and Turn Feedback Into Actionable Insights
MarketWrk
MarketWrk automates retail price monitoring and MAP violation alerts, transforming data into actionable pricing intelligence for CPG brands.
Opal44
Opal44 delivers clear, AI-powered insights from your website traffic data in plain English, making analytics accessible.
Fusedash
Fusedash transforms raw data into intuitive dashboards and charts, empowering teams to act on insights swiftly.
finban
finban simplifies liquidity planning, empowering confident decisions on hiring, taxes, and investments without Excel.
Zignt
Zignt creates, sends, and signs legally binding contracts instantly.
SpechAI
SpechAI is your AI speech coach for instant feedback and confident public speaking practice.