aVenture vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
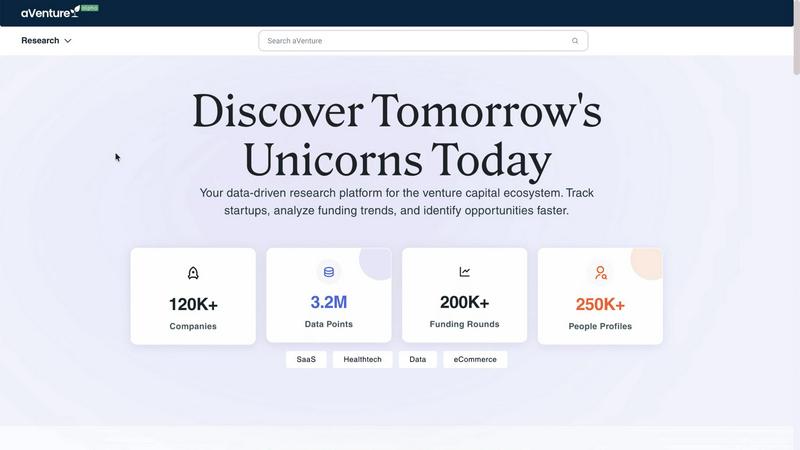
aVenture is an AI platform that empowers users to research startups, track funding, and analyze competitors efficiently.
Last updated: March 1, 2026
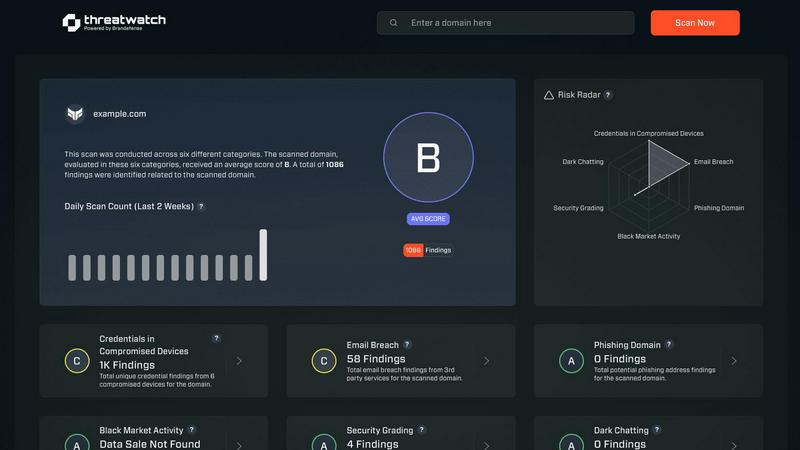
Threat Watch
Quickly assess your cybersecurity health with Threat Watch's actionable insights on compromised accounts and devices.
Last updated: March 1, 2026
Visual Comparison
aVenture
Threat Watch
Feature Comparison
aVenture
Comprehensive Company Tracking
aVenture tracks over 107,000 venture-backed companies globally, providing in-depth insights into their ownership structures, funding histories, and competitive positioning. This feature allows users to surface critical insights that institutional investors rely on.
Real-Time News Summaries
The platform’s AI analyst scans and summarizes the latest news, offering real-time insights into company developments and market trends. Users benefit from concise updates that highlight risks and opportunities, enabling proactive decision-making.
Extensive Funding Data
With access to $12.7 trillion in total funding data, aVenture allows users to analyze funding rounds and identify emerging opportunities. This feature enhances the ability to track investment trends and make strategic choices based on historical funding patterns.
Investor Mapping
aVenture provides detailed investor mappings, showcasing nearly 30,000 investors, their investment preferences, and historical data. This feature is crucial for professionals looking to build relationships with potential investors or understand the competitive landscape better.
Threat Watch
Comprehensive Cyber Health Assessment
Threat Watch provides a detailed evaluation of an organization’s cybersecurity posture by continuously scanning for vulnerabilities, compromised credentials, and potential threats, ensuring a holistic view of security health.
Automated Threat Intelligence
The platform automates the gathering and analysis of complex threat intelligence, reducing manual workload and providing real-time insights that help organizations identify emerging threats and assess their risk levels swiftly.
Prioritized Action Plan
By consolidating fragmented threat data, Threat Watch generates a single prioritized action plan. This enables organizations to focus on the most critical risks and respond effectively to mitigate potential damage.
Dark Web Monitoring
Threat Watch continuously monitors dark web activities to identify compromised credentials and breached accounts, allowing organizations to take immediate action to protect their assets from potential exploitation.
Use Cases
aVenture
Founders Preparing for Fundraising
Founders can utilize aVenture to gather insights on potential investors and funding trends, helping them craft tailored pitches that resonate with their target audience, thereby increasing their chances of securing investment.
Investment Analysts Conducting Due Diligence
Investment analysts can leverage the platform's deep company insights and funding data to perform thorough due diligence. This ensures that all potential risks and opportunities are considered before making investment decisions.
Business Development Teams Scouting Partners
Business development teams can identify and analyze potential partners through aVenture’s comprehensive data on companies and investors. This helps in forming strategic alliances that can enhance business growth.
Operators Monitoring Competitive Landscapes
Operators can track their competitors and industry trends using aVenture’s real-time news summaries and company insights. This enables them to stay ahead of the competition and adapt strategies according to market changes.
Threat Watch
IT Security Monitoring
IT security teams can leverage Threat Watch to continuously monitor their digital assets for vulnerabilities and threats. The platform provides real-time alerts, helping teams respond swiftly to emerging risks.
Risk Management
Risk managers can use Threat Watch to assess the overall cybersecurity health of the organization. The actionable insights provided enable informed decision-making and risk prioritization to protect sensitive data.
Incident Response Planning
Organizations can utilize Threat Watch to develop effective incident response plans. The platform’s real-time threat intelligence assists teams in preparing for potential security incidents, minimizing response times and impact.
Compliance Assurance
Threat Watch aids organizations in maintaining compliance with industry regulations by providing comprehensive assessments of cybersecurity practices. This ensures that organizations meet required standards while safeguarding their data.
Overview
About aVenture
aVenture is an institutional-grade venture intelligence platform that offers deep research capabilities on private companies and venture capital investing. Designed to provide comprehensive, data-driven insights, it tracks over 109,000 active companies, $12.7 trillion in total funding, and nearly 30,000 investors. The platform transforms vast amounts of raw data into actionable intelligence, utilizing a proprietary AI analyst that scans the latest news and coverage. This AI delivers concise summaries of company traction, highlights potential risks, and explains how recent events impact businesses. aVenture empowers a diverse range of professionals, including founders preparing for fundraising, investment analysts conducting due diligence, business development teams scouting partners, and operators monitoring competitive landscapes. By consolidating company profiles, funding histories, investor mappings, and real-time signals into a single workspace, aVenture enables users to make informed and confident decisions in the private markets.
About Threat Watch
Threat Watch is a unified cybersecurity intelligence platform that empowers organizations to gain a clear and actionable view of their digital security posture. Designed for IT security teams, risk managers, and business leaders, it shifts the focus from reactive security to proactive risk management. Threat Watch continuously analyzes an organization's assets, vulnerabilities, and exposures across critical security categories, providing a comprehensive cyber health assessment. Its core value proposition lies in its speed and clarity; the platform automates intricate threat intelligence gathering and analysis, delivering real-time insights. This enables users to identify, prioritize, and mitigate risks more efficiently. By consolidating data on compromised credentials, breached accounts, phishing addresses, and dark web exposures, Threat Watch transforms fragmented threat data into a prioritized action plan, ensuring organizations can act quickly to safeguard their digital environments.
Frequently Asked Questions
aVenture FAQ
What types of companies does aVenture track?
aVenture tracks over 107,000 active venture-backed companies across various industries, providing comprehensive insights into their performance and funding histories.
How does aVenture's AI analyst work?
The AI analyst scans and summarizes the latest news and developments related to tracked companies. It highlights key traction points, potential risks, and the implications of recent events, delivering actionable intelligence to users.
Who are the primary users of aVenture?
The platform is designed for a diverse range of professionals, including founders preparing for fundraising, investment analysts performing due diligence, business development teams scouting partnerships, and operators monitoring competitive landscapes.
Can I access real-time funding data on aVenture?
Yes, aVenture provides real-time access to extensive funding data, allowing users to analyze funding rounds and identify emerging investment opportunities as they happen.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, including those in finance, healthcare, and technology sectors, where cybersecurity is critical to protecting sensitive information and maintaining compliance.
How does Threat Watch automate threat intelligence?
The platform utilizes advanced algorithms and machine learning to automate the collection and analysis of threat data from various sources, significantly reducing the time and effort required for manual threat assessments.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to integrate seamlessly with existing cybersecurity tools and platforms, allowing organizations to enhance their security posture without disrupting current workflows.
What is the process for starting with Threat Watch?
Organizations can easily initiate a free scan through the Threat Watch platform. This initial assessment provides valuable insights into their cybersecurity health, helping them understand their risk landscape.
Alternatives
aVenture Alternatives
aVenture is an AI-driven venture intelligence platform tailored for comprehensive research on private companies and venture capital investing. It provides users with actionable insights into the startup ecosystem, offering access to extensive data on active companies, funding, and investors. Users commonly seek alternatives due to factors such as pricing, varying features, or specific platform needs that may better align with their research objectives or workflows. When choosing an alternative, consider aspects like the depth of the company database, the sophistication of analytical tools, ease of use, and the ability to generate meaningful insights from data.
Threat Watch Alternatives
Threat Watch is a comprehensive cybersecurity intelligence platform that empowers organizations to assess their digital security health with actionable insights. Designed for IT security teams, risk managers, and business leaders, it automates complex threat intelligence gathering and offers real-time assessments of vulnerabilities and exposures. Users often seek alternatives due to factors such as pricing, unique feature sets, or specific platform compatibility needs that better align with their organizational goals. When considering alternatives, look for platforms that provide robust threat intelligence, real-time monitoring capabilities, and an intuitive user interface. It's essential to evaluate the comprehensiveness of the cyber health assessments and whether the solution can effectively prioritize risks based on severity and context to ensure proactive risk management.
