iGPT vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
iGPT gives AI agents secure, context-aware answers from your team's email data.
Last updated: February 28, 2026
Threat Watch
Quickly assess your cybersecurity health with Threat Watch's actionable insights on compromised accounts and devices.
Last updated: March 1, 2026
Visual Comparison
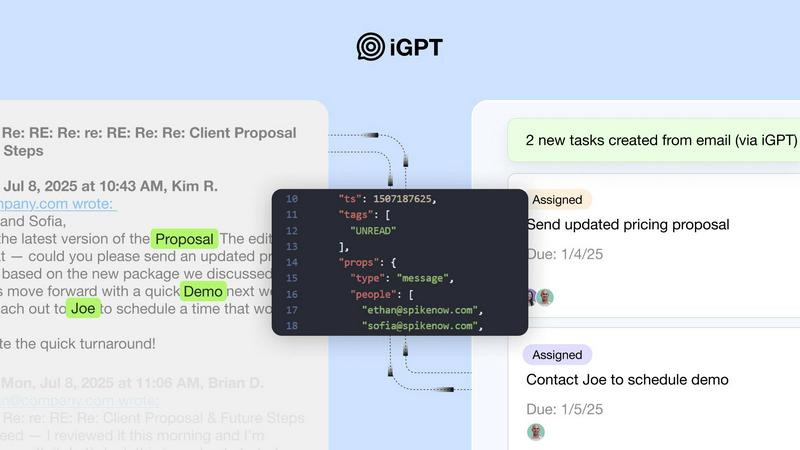
iGPT
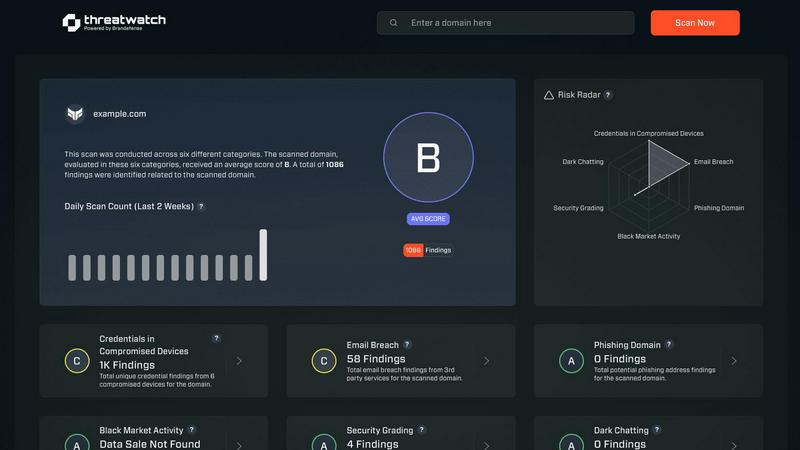
Threat Watch
Feature Comparison
iGPT
Unified Contextual Endpoint
Replace complex multi-step retrieval systems with a single natural language API request. iGPT's unified endpoint seamlessly handles retrieval, context shaping, and reasoning in one integrated pipeline, delivering answers ready for automation without any prompt engineering or manual pipeline management required.
Deep Email & Attachment Processing
iGPT automatically and deeply indexes all email data, including complex threads with multiple participants. It also processes attachments, extracting text, data, and structure from documents, PDFs, and spreadsheets to provide a complete view of the conversation's context and content.
Hybrid Retrieval with Citations
The system employs a sophisticated hybrid retrieval method combining semantic, keyword, and filtered search, which is then scored and re-ranked in one call. Every answer is returned with direct citations back to the source emails and attachments, ensuring verifiability and trust.
Enterprise-Grade Security & Auditability
Built with strict security principles, iGPT offers zero data training, OAuth-only processing with Role-Based Access Control (RBAC), and zero data retention. Each inference is processed in memory, and a full audit trail ensures all actions are traceable, keeping data under your company's control.
Threat Watch
Comprehensive Cyber Health Assessment
Threat Watch provides a detailed evaluation of an organization’s cybersecurity posture by continuously scanning for vulnerabilities, compromised credentials, and potential threats, ensuring a holistic view of security health.
Automated Threat Intelligence
The platform automates the gathering and analysis of complex threat intelligence, reducing manual workload and providing real-time insights that help organizations identify emerging threats and assess their risk levels swiftly.
Prioritized Action Plan
By consolidating fragmented threat data, Threat Watch generates a single prioritized action plan. This enables organizations to focus on the most critical risks and respond effectively to mitigate potential damage.
Dark Web Monitoring
Threat Watch continuously monitors dark web activities to identify compromised credentials and breached accounts, allowing organizations to take immediate action to protect their assets from potential exploitation.
Use Cases
iGPT
Intelligent Email Assistants
Build AI agents that can draft, prioritize, summarize, and act on emails with a complete understanding of the entire thread history, participant roles, and attached documents, dramatically improving productivity and response quality.
Customer Support Copilots
Empower support teams with agents that instantly reconstruct the full customer story across long, messy email chains. These copilots can understand tone shifts, track issues, and reference attachments to provide accurate, context-rich support.
Workflow & CRM Automation
Automatically turn email conversations into structured data for other systems. Extract action items, deadlines, approvals, and deal momentum to create tasks in project tools or update records in CRM platforms like Salesforce, directly from email threads.
Compliance & Audit Trail Generation
Automate the tracking of critical communications for legal and regulatory compliance. iGPT can trace feedback, decisions, approvals, and rationale back to the original email and attachment sources, creating a reliable and searchable audit trail.
Threat Watch
IT Security Monitoring
IT security teams can leverage Threat Watch to continuously monitor their digital assets for vulnerabilities and threats. The platform provides real-time alerts, helping teams respond swiftly to emerging risks.
Risk Management
Risk managers can use Threat Watch to assess the overall cybersecurity health of the organization. The actionable insights provided enable informed decision-making and risk prioritization to protect sensitive data.
Incident Response Planning
Organizations can utilize Threat Watch to develop effective incident response plans. The platform’s real-time threat intelligence assists teams in preparing for potential security incidents, minimizing response times and impact.
Compliance Assurance
Threat Watch aids organizations in maintaining compliance with industry regulations by providing comprehensive assessments of cybersecurity practices. This ensures that organizations meet required standards while safeguarding their data.
Overview
About iGPT
iGPT is an enterprise-grade email intelligence API that transforms the unstructured data within email communications and attachments into structured, actionable intelligence for AI agents and automated workflows. It solves a critical gap where most AI systems fail: reliably accessing and understanding the complex context of email threads, documents, and historical conversations. Designed for developers and enterprises, iGPT provides a secure, unified gateway to deep email context through a single API call. This eliminates the immense engineering burden of building and maintaining custom pipelines for parsing, chunking, indexing, and prompt tuning. By delivering trusted, context-aware answers with full citations, iGPT enables businesses to confidently deploy intelligent automation for sales, customer support, operations, and compliance, turning the chaos of email into a powerful, structured data source.
About Threat Watch
Threat Watch is a unified cybersecurity intelligence platform that empowers organizations to gain a clear and actionable view of their digital security posture. Designed for IT security teams, risk managers, and business leaders, it shifts the focus from reactive security to proactive risk management. Threat Watch continuously analyzes an organization's assets, vulnerabilities, and exposures across critical security categories, providing a comprehensive cyber health assessment. Its core value proposition lies in its speed and clarity; the platform automates intricate threat intelligence gathering and analysis, delivering real-time insights. This enables users to identify, prioritize, and mitigate risks more efficiently. By consolidating data on compromised credentials, breached accounts, phishing addresses, and dark web exposures, Threat Watch transforms fragmented threat data into a prioritized action plan, ensuring organizations can act quickly to safeguard their digital environments.
Frequently Asked Questions
iGPT FAQ
How does iGPT handle data privacy and security?
iGPT is built on a foundation of enterprise-grade security. It practices zero data training, meaning your data is never used to train models. It uses OAuth-only processing with RBAC, enforces zero data retention (processing happens in memory), and provides a full audit trail, ensuring data never leaves your control.
What makes iGPT different from using a generic LLM on email text?
Generic LLMs lack the specialized understanding of email structure, threading, and attachment context. iGPT provides a complete pipeline that deeply indexes, reconstructs threads, processes attachments, and performs optimized retrieval to deliver accurate, cited answers from messy email data through one simple call, eliminating months of custom engineering.
Can iGPT process data from multiple email sources?
Yes, iGPT is designed to connect to and unify data from various enterprise email sources. It deeply indexes emails and attachments from these connected sources, allowing a single API query to retrieve context from across all of them, creating a unified intelligence layer.
What is the Context Engineering Framework (CEF)?
The Context Engineering Framework (CEF) is iGPT's performance and quality tier system. It allows developers to choose the optimal balance of speed, cost, and reasoning depth for their specific use case by selecting different CEF tiers (e.g., cef-1-normal) when making an API request.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, including those in finance, healthcare, and technology sectors, where cybersecurity is critical to protecting sensitive information and maintaining compliance.
How does Threat Watch automate threat intelligence?
The platform utilizes advanced algorithms and machine learning to automate the collection and analysis of threat data from various sources, significantly reducing the time and effort required for manual threat assessments.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to integrate seamlessly with existing cybersecurity tools and platforms, allowing organizations to enhance their security posture without disrupting current workflows.
What is the process for starting with Threat Watch?
Organizations can easily initiate a free scan through the Threat Watch platform. This initial assessment provides valuable insights into their cybersecurity health, helping them understand their risk landscape.
Alternatives
iGPT Alternatives
iGPT is an enterprise-grade email intelligence API that transforms unstructured email and attachment data into structured, context-aware answers for AI agents and workflows. It belongs to the business intelligence category, specifically solving for secure, reliable access to team communication data. Users may look for alternatives for various reasons, including budget constraints, specific feature requirements not covered, or a need for a different deployment model. Some may seek a broader platform or a solution integrated into an existing tech stack. When evaluating alternatives, consider core capabilities like depth of email and attachment processing, security and compliance standards, ease of API integration, and the system's ability to deliver accurate, contextual answers from complex communication threads.
Threat Watch Alternatives
Threat Watch is a comprehensive cybersecurity intelligence platform that empowers organizations to assess their digital security health with actionable insights. Designed for IT security teams, risk managers, and business leaders, it automates complex threat intelligence gathering and offers real-time assessments of vulnerabilities and exposures. Users often seek alternatives due to factors such as pricing, unique feature sets, or specific platform compatibility needs that better align with their organizational goals. When considering alternatives, look for platforms that provide robust threat intelligence, real-time monitoring capabilities, and an intuitive user interface. It's essential to evaluate the comprehensiveness of the cyber health assessments and whether the solution can effectively prioritize risks based on severity and context to ensure proactive risk management.
