CMMC ROI vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
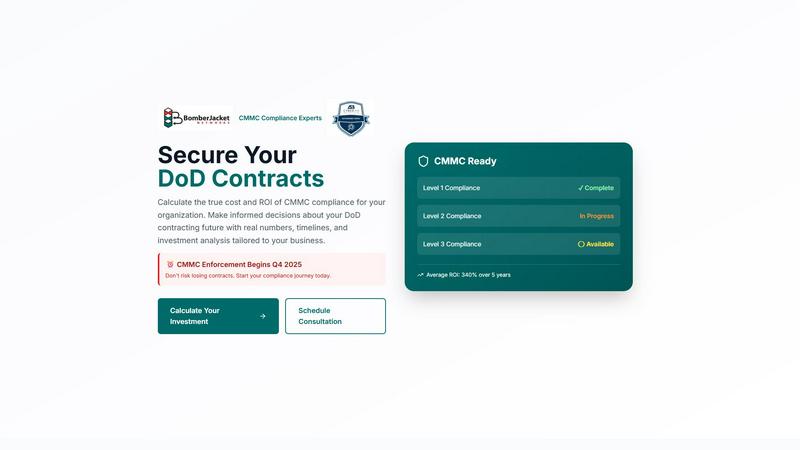
CMMC ROI
CMMC ROI calculates compliance costs and ROI, empowering smarter DoD contracting decisions for your business.
Last updated: March 1, 2026
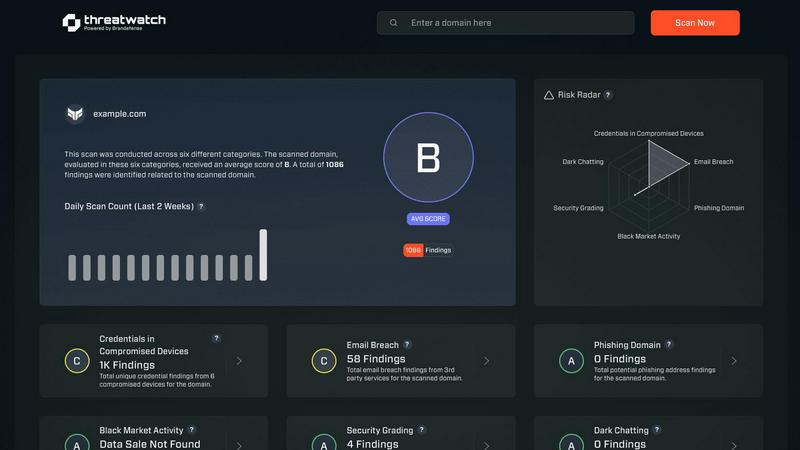
Threat Watch
Quickly assess your cybersecurity health with Threat Watch's actionable insights on compromised accounts and devices.
Last updated: March 1, 2026
Visual Comparison
CMMC ROI
Threat Watch
Feature Comparison
CMMC ROI
Investment Calculator
The CMMC ROI Investment Calculator allows contractors to input their specific company data, including size, annual revenue, and required CMMC level. This feature generates tailored investment estimates, helping businesses understand the financial implications of compliance.
ROI Analysis
CMMC ROI provides a detailed ROI analysis, calculating the return on investment based on protected value and total estimated investment. Users can visualize the financial benefits of compliance, including potential contract value at risk and the average average ROI over five years.
Compliance Progress Tracking
This feature enables users to monitor their compliance journey effectively. It outlines the steps required for CMMC certification and allows contractors to track their progress, ensuring they remain on schedule for certification before the 2025 deadline.
Critical Risk Assessment
CMMC ROI includes a critical risk assessment that highlights the risks associated with non-compliance. By detailing the potential losses from breaches and false claims, this feature underscores the necessity of achieving CMMC certification for DoD contractors.
Threat Watch
Comprehensive Cyber Health Assessment
Threat Watch provides a detailed evaluation of an organization’s cybersecurity posture by continuously scanning for vulnerabilities, compromised credentials, and potential threats, ensuring a holistic view of security health.
Automated Threat Intelligence
The platform automates the gathering and analysis of complex threat intelligence, reducing manual workload and providing real-time insights that help organizations identify emerging threats and assess their risk levels swiftly.
Prioritized Action Plan
By consolidating fragmented threat data, Threat Watch generates a single prioritized action plan. This enables organizations to focus on the most critical risks and respond effectively to mitigate potential damage.
Dark Web Monitoring
Threat Watch continuously monitors dark web activities to identify compromised credentials and breached accounts, allowing organizations to take immediate action to protect their assets from potential exploitation.
Use Cases
CMMC ROI
Small Contractor Compliance
A small contractor can use CMMC ROI to calculate the investment needed for Level 2 compliance. By entering their company details, they can receive a personalized investment analysis and understand how compliance impacts their contract eligibility.
Medium Contractor Risk Mitigation
Medium-sized contractors can leverage CMMC ROI to assess their financial risks associated with cybersecurity breaches. By calculating potential costs avoided through CMMC certification, they can make informed decisions on investing in compliance.
Large Contractor Contract Security
Large contractors can utilize CMMC ROI to protect their substantial DoD revenue. The tool helps them identify the total investment required for Level 3 compliance and the potential return, ensuring they maintain their competitive edge.
Technology Firm Certification Journey
A technology firm with multiple DoD contracts can use CMMC ROI to map out its compliance journey. By understanding the costs and timelines associated with Level 2 certification, they can effectively allocate resources to meet the 2025 compliance deadline.
Threat Watch
IT Security Monitoring
IT security teams can leverage Threat Watch to continuously monitor their digital assets for vulnerabilities and threats. The platform provides real-time alerts, helping teams respond swiftly to emerging risks.
Risk Management
Risk managers can use Threat Watch to assess the overall cybersecurity health of the organization. The actionable insights provided enable informed decision-making and risk prioritization to protect sensitive data.
Incident Response Planning
Organizations can utilize Threat Watch to develop effective incident response plans. The platform’s real-time threat intelligence assists teams in preparing for potential security incidents, minimizing response times and impact.
Compliance Assurance
Threat Watch aids organizations in maintaining compliance with industry regulations by providing comprehensive assessments of cybersecurity practices. This ensures that organizations meet required standards while safeguarding their data.
Overview
About CMMC ROI
CMMC ROI is an essential tool designed to assist Department of Defense (DoD) contractors in understanding and calculating the true costs and returns associated with Cybersecurity Maturity Model Certification (CMMC) compliance. This comprehensive solution, offered by BomberJacket Networks—an authorized C3PAO and service-disabled veteran-owned business—leverages over 20 years of cybersecurity expertise to craft tailored compliance strategies. With CMMC enforcement set to begin in Q4 2025, CMMC ROI equips organizations with the necessary insights to make informed decisions about their future in DoD contracting. By providing accurate calculations of costs, timelines, and investment analyses, CMMC ROI empowers businesses to secure vital contracts, mitigate risks, and improve their competitiveness in the defense contracting landscape.
About Threat Watch
Threat Watch is a unified cybersecurity intelligence platform that empowers organizations to gain a clear and actionable view of their digital security posture. Designed for IT security teams, risk managers, and business leaders, it shifts the focus from reactive security to proactive risk management. Threat Watch continuously analyzes an organization's assets, vulnerabilities, and exposures across critical security categories, providing a comprehensive cyber health assessment. Its core value proposition lies in its speed and clarity; the platform automates intricate threat intelligence gathering and analysis, delivering real-time insights. This enables users to identify, prioritize, and mitigate risks more efficiently. By consolidating data on compromised credentials, breached accounts, phishing addresses, and dark web exposures, Threat Watch transforms fragmented threat data into a prioritized action plan, ensuring organizations can act quickly to safeguard their digital environments.
Frequently Asked Questions
CMMC ROI FAQ
What is CMMC ROI?
CMMC ROI is a tool designed to help DoD contractors calculate the costs and returns associated with CMMC compliance, enabling informed decision-making regarding their contracting future.
How does the investment calculator work?
The investment calculator allows users to input specific data about their company, such as size and revenue. It then generates a tailored investment estimate for achieving compliance with CMMC standards.
Why is CMMC compliance important?
CMMC compliance is essential for securing DoD contracts. It helps mitigate risks associated with cybersecurity breaches and enhances a contractor’s competitiveness in the defense contracting space.
What are the key benefits of using CMMC ROI?
Key benefits include tailored investment analyses, ROI projections, progress tracking for compliance, and critical risk assessments, all of which empower contractors to make informed decisions about their cybersecurity investments.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, including those in finance, healthcare, and technology sectors, where cybersecurity is critical to protecting sensitive information and maintaining compliance.
How does Threat Watch automate threat intelligence?
The platform utilizes advanced algorithms and machine learning to automate the collection and analysis of threat data from various sources, significantly reducing the time and effort required for manual threat assessments.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to integrate seamlessly with existing cybersecurity tools and platforms, allowing organizations to enhance their security posture without disrupting current workflows.
What is the process for starting with Threat Watch?
Organizations can easily initiate a free scan through the Threat Watch platform. This initial assessment provides valuable insights into their cybersecurity health, helping them understand their risk landscape.
Alternatives
CMMC ROI Alternatives
CMMC ROI is a comprehensive solution designed for Department of Defense contractors, enabling them to assess compliance costs and return on investment related to Cybersecurity Maturity Model Certification. As a product that falls under the business intelligence category, it empowers organizations to navigate the complexities of CMMC compliance effectively. Users often seek alternatives due to factors such as pricing, feature sets, and specific platform compatibility. When choosing an alternative, it is crucial to consider the tool's ability to deliver clear ROI calculations, provide detailed investment breakdowns, and offer comprehensive risk assessment insights that align with the unique needs of your organization.
Threat Watch Alternatives
Threat Watch is a comprehensive cybersecurity intelligence platform that empowers organizations to assess their digital security health with actionable insights. Designed for IT security teams, risk managers, and business leaders, it automates complex threat intelligence gathering and offers real-time assessments of vulnerabilities and exposures. Users often seek alternatives due to factors such as pricing, unique feature sets, or specific platform compatibility needs that better align with their organizational goals. When considering alternatives, look for platforms that provide robust threat intelligence, real-time monitoring capabilities, and an intuitive user interface. It's essential to evaluate the comprehensiveness of the cyber health assessments and whether the solution can effectively prioritize risks based on severity and context to ensure proactive risk management.
